The article was updated on 17 October 2022 by Inna Logunova.
The terms “blockchain” and “distributed ledger technology (DLT)” are very often used as synonyms. Guess what: they are not! So, if you don’t want to look like a weirdo in front of your colleagues, read on.
What is distributed ledger technology?
Distributed ledger technology (DLT) is a way of storing information. Let’s analyze it word by word.
A brief history of distributed ledger technology
So, first, there is “ledger”. A long time ago, when people had no idea about the Internet, electronic cash registers, and other wibbly-wobbly hi-tech, they would put information about their transactions in a regular book called a ledger. Imagine: you go to a bank to ask for a credit, and the clerk makes a record on paper about how much money you took and when you need to restore it.
Is there any problem with storing information like this? A bunch of them, of course.
-
Theft. Anyone can steal a ledger, delete or change the information: your creditor, other bank employees or even you.
-
Human factor. It’s easy to write $100,000 instead of 10,000 intentionally or by mistake, which will be an unpleasant surprise for you as a borrower.
-
Force Majeure. All the recordings can get destroyed by natural reasons like a flood or a fire.
The thing is that keeping records on a regular server or cloud database today is not much different in terms of security than just storing it on paper. Someone can hack it, or the server can crash by itself (the problem of Single Point of Failure).
So, keeping all the eggs in one basket is not a good solution. What shall we do?
Make copies.
This is where the word “distributed” steps into the game.
Distributed means that the information from the book is kept, administered and used by all members. It’s still a book, or to be more precise, a database, but it’s spread across all the participants of the DLT network. These are also called nodes.
How do you ensure that the same data is seen across the network without any central authority in power?
In 1991, the researchers Stuart Haber and W. Scott Stornetta asked themselves the same question. They proposed practical methods for time-stamping digital data.
Follow their logic:
- In the digital world, everything is modifiable. Usually, you have no chance to see whether the data was changed. To fight this, you need to time-stamp the information so that all the changes could be trackable.
- You need to time-stamp actual bits of content, not the moment when the file that stores this data was created.
- Also, the date and time of the time-stamp must not be forgeable. The scientists introduce hashes and digital signatures as possible means to solve this problem.
These principles basically gave birth to DLT.
In 2002, David Mazières and Dennis Shasha continued to develop the concept, studying how to store data in blocks. They were working on a protocol of a multi-user network file system called SUNDR (Secure Untrusted Data Repository). The fruits of their work laid the ground for the blockchain of today. After the appearance and spread of blockchain, the history of DLT became the history of blockchain.
In a distributed ledger system, all nodes have their copy of the ledger and update information independently.
To make a change, they need to go through a mechanism of consensus where the nodes collectively agree for the change to be introduced. This is how we make sure that the copy of the ledger is the same in all the nodes.
There is a multitude of ways to do this, and the choice of the consensus mechanism depends on how large tolerance for faulty actors do you wish your system to have and several other constraints. While consensus can technically be achieved with just a vector clock, it is much more popular to use protocols like Paxos and pBFT.
So, all in all, the definition of distributed ledger goes as follows:
A distributed ledger technology is a decentralized database distributed across different nodes of the network. Every node views all the records in question and processes every transaction. The nodes collectively vote on every item’s veracity guaranteeing trust and transparency under certain conditions.
Benefits of distributed ledger technology
DLT has gained a wide popularity thanks to its multiple benefits over centralized data storage systems.
-
Transparency and immutability. Unlike in a centralized system, all nodes enjoy equal rights over the data. All the decisions are made collectively. DLT provides an immutable and verifiable audit trail of all operations.
-
Attack resistance. DLT is a more cyber-attack resilient system than traditional centralized databases because it’s distributed. There is no single point of attack, which makes the attempts to hack such systems too expensive and useless.
Blockchain vs. DLT
.jpg)
Now let us get back to the blockchain. Why does everybody mix these two terms?
The answer is that blockchain is indeed a distributed ledger system. Blockchain users also have decentralized control over data, and many nodes participate in the distribution, administration, and change of data.
What matters is that blockchain is a specific type of DLT. It looks like a sequence of blocks of information. Each of them depends on the previous block and the following, which does imitate the construction of a chain.
Here are the differences between blockchain and DLT:
-
Available operations. In a traditional database technology, four operations are available: Create, Retrieve, Update and Delete (CRUD). In a blockchain, you can only use Create and Retrieve operations.
-
Block structure. Blockchain represents data as a chain of blocks, which is not mandatory for other types of DLT.
-
Sequence. Distributed ledger technology doesn’t have to follow the block after block structure of the blockchain.
-
Tokens. Blockchain is generally a token economy, but DLT doesn’t require their usage.
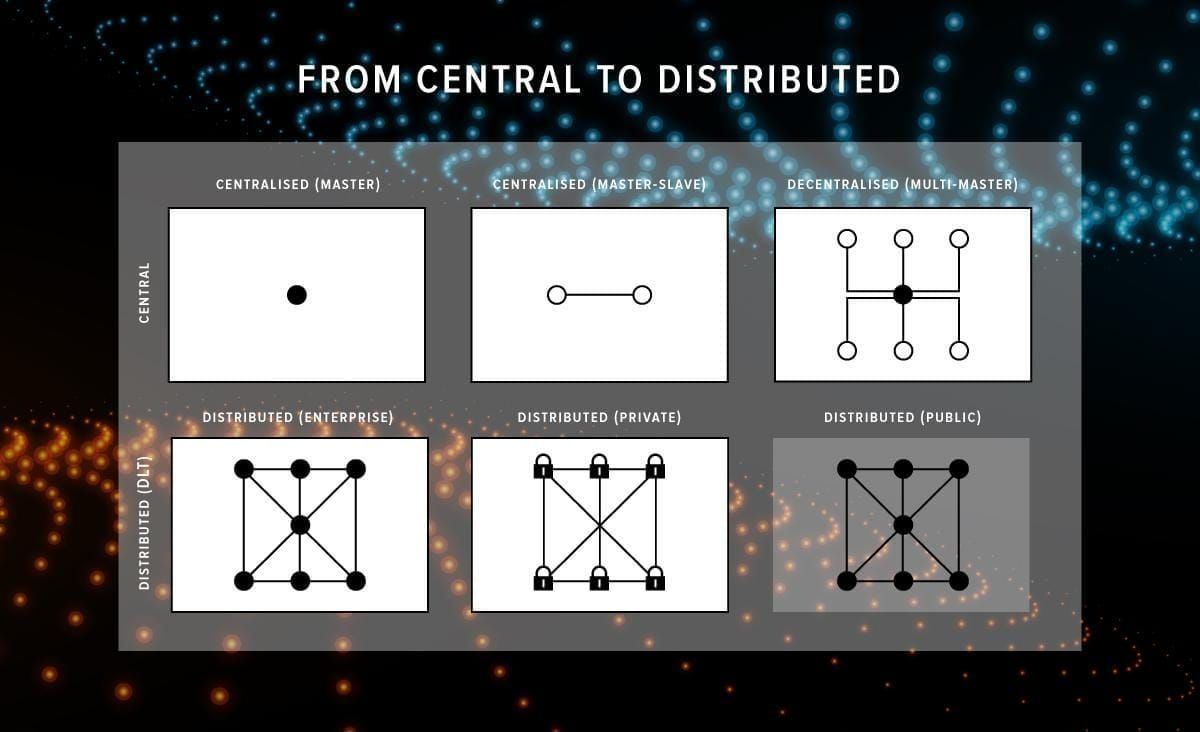
Different types of DLT
Blockchain is the most popular type of DLT. However, it’s not the only one.
The most popular types of DLT that are used in industry today can be divided into three groups:
-
Public. This is a decentralized system where any two parties regardless of their location can transact. Public DLT relies on the consensus of all the nodes.
-
Private. Often used by enterprises as a corporate database. It’s a permissioned network meaning that different ledgers are still synchronized across the nodes. However, there is an owner who has the power to decide who will get access to the network.
-
Consortium. Consortium DLT is used by an association of companies that share equal rights over the network. The system lets multiple businesses use the DLT as a decentralized system. These are also called federated DLTs.
Case study: practical applications of distributed ledger technology
Cardano Settlement Layer
Serokell is one of the teams of independent researchers and software engineers who developed the Cardano project. It is an open-source decentralized public blockchain. The purpose of Cardano was to provide the users with a smart contract platform that overcame common security flaws, had decreased transaction costs and improved network speed.

We developed the Cardano Settlement Layer cryptocurrency and a wallet for CSL.
Cardano uses a Proof-of-Stake consensus algorithm. This choice allowed to introduce some fresh features to CSL. Let’s talk about them more in detail.
Delegation
This feature allows a node to be offline but still have an impact on the system. Delegation isn’t compatible with PoW where everybody should be present in order to vote. There are two types of this feature that the users can benefit from using Cardano.
Heavy delegation
How does it work? Imagine being in a board of directors of an enterprise. All the members have shares, attend meetings and vote on decisions regarding the company.
- If one of them can’t attend a meeting, they trust somebody to vote on their behalf. For that, a warrant (or a proxy, in our case) is needed. It will be sent to other members of the board to let them know that somebody else is eligible to vote on behalf of that member.
- If the member that was absent arrives to the next meeting, they need to “revoke” the proxy, sending a signed letter to each member and stating that it’s not valid anymore.
Light delegation
Another option is to give the proxy only to your representative who will show it to the others on demand whenever needed to vote on your behalf. If you come to the meeting, the others will just ignore the proxy.
Update system
This feature allows all users to vote for proposed updates. Any user can suggest an update to the system. The others will have a look at it, make sure it’s safe and won’t allow anybody to abuse the system. If it’s okay, they cast their shares for the update. So, the system is self-regulated: a user proposes updates, other users vote. If there are enough votes, the system will be updated.
- For instance, someone might want to contribute to Ouroboros. They can write their code and post it for others to consider. If the board of directors votes for it, this piece of code automatically patches the existing code.
Smart contracts
You can write code, send it to all nodes in the system, and the code will run on them. Every node will check whether the code is correct, for example, that it doesn’t waste money it’s not allowed to spend.
This concept provides an ability to write applications over CSL. For example, you can write your own gambling platform. Its advantage is that the processing of the game happens not on one server, which may be corrupted but on multiple nodes that execute the code. Even if one of the nodes is corrupted, the others will say: you argue the results of the execution are this, but we think otherwise. Since they prevail, nobody counts the corrupted node.
Overall, CSL has tried to bring up a scientific-driven approach to development for the construction of a whole new community. After all, cryptocurrency is much more than just technical decisions, algorithms and coding. It’s a community of people who believe they are doing the right thing, which may help to build a better fintech future for the whole world.
Myths about DLT
As with any technology, there are some risks associated with DLT. However, more issues result from misunderstanding the concept. Here are some of the most common myths.
In some cases, the private key can be discovered using a public one
Within Blockchain and DLT networks, public and private keys serve an essential purpose - they are what enable the network to verify whether someone wishing to execute a transaction, such as sending a token, has the authority to do so.
It’s close to impossible to guess the private key based on the public one. Otherwise, the entire cryptographic system, which has been around for almost half a century, wouldn’t work. Your private key is secure unless you accidentally make it publicly available. To better understand how a public-key cryptosystem operates, read this Wikipedia article about RSA, which is one example of such a system. The main problem is the opposite: if you lose your private key, no one can recover it, and you will lose access everything that’s registered under this key.
Identity exposure can occur due to the use of a DLT
A distributed system does require verification for new operations, but this can be done without disclosing participants’ personal data. By introducing unique IDs, not related to the particular persona, DLT operations can be implemented without identity exposure. There is no need to reveal the identity of people involved in an operation. Check out labs.hyperledger.org for a more detailed explanation.
Funds in a smart contract can be locked due to an unforeseen condition in the code
In fact, this myth is true, this situation has occurred a few times due to a bug. Errors in code can occur in any software, but smart contracts are written with strong emphasis on security. The purpose of locking funds in a smart contract is always to protect them from suspicious activity. Like any financial software, smart contracts are a likely target for cybercriminals and should be subject to increased quality control and security audit to guarantee code correctness and protection from security risks.
DLT suffers from a lack of regulation
One of the issues is that this technology offers something totally different than the traditional centralized system with a regulator at the top. Understanding that such a decentralized system can function without regulators and an assigned governor, and at the same time, be secure, is the biggest challenge for the financial community to accept this new technology as a basis for economic cooperation.
The main problem with introducing DLT is that financial and government authorities want a particular organization responsible for GDPR or CCPA violations and personal data leakage, whereas DLT is based on the opposite concept – distribution of authority.
Summing up
Now you can tell the difference between a DLT and a blockchain. You’ve learned about the advantages and disadvantages of blockchain as opposed to other types of distributed ledger systems. These technologies represent a new way of storing and processing data that is being adopted by more and more companies across different industries worldwide like healthcare, law, education and so on.
Stay tuned to our blog and follow us on social networks like Twitter for more engaging materials about cutting-edge technologies.
Serokell offers professional blockchain development services. We will help you launch secure decentralized systems. Let’s discuss your needs!


.jpg)
.jpg)
.jpg)
.jpg)

